2014 will be remembered as the Year of the hack.
Sony, Target, Home Depot, UPS, even Victoria couldn’t keep the Secret.
The list:
http://www.idtheftcenter.org/images/breach/DataBreachReports_2014.pdf
This article will tell you how to stay off.
What Has Already Been Tried
First let’s have a look at what’s already being done.
The perimeter has shattered. Firewalls won’t stop someone who has credentials–attacks within the interior of a network.
“Myth: Firewalls make your data secure. In fact, 40% of Internet break-ins occur in spite of a firewall being in place.“
Data Security Challenges – Oracle9i Security Review
II. Stong Authentication / Multi-factor Authentication / Single Sign-on
Often times bad things are committed by those with proper credentials. Do not base your entire defense on the front door.
“Neither top secret clearance, sophisticated authentication nor the most advanced encrypted information systems can necessarily stop an intended breach action. These security procedures are not designed to detect real-time actions and anomalous business processes from authorized personnel. These practices are just the “moat around the castle” approach upon which most current cybersecurity technologies are based. Current national security breaches clearly show we need to do more.”
Is Cyber Security an Inside Job? – Larry Karisny – Digital Communities
Doesn’t stop attacks in-flight. By the time a new virus has been identified, two more have spawned.
“In the bigger picture, furthermore, the anti-virus software was irrelevant, contends Chester Wisniewski, a senior security advisor at anti-virus vendor Sophos. “A smart attacker in a targeted environment will always bypass your anti-virus,” he says, and especially if they’re trying to take down a retailer the size of Home Depot.“
Analysis: Home Depot Breach Details – Mathew J Schwartz – Bank Info Security
These practices aren’t necessarily wrong, but they aren’t fixing the problem either.
The Problem
So what exactly is the problem?
A determined attack will gain access to your network – count on it. It’s impossible for you to harden every entry point. Find a way to minimize damage once the inevitable unauthorized entry occurs.
“Organizations should stop thinking about breach prevention, accept their going to be breached, change their mindset, and think about how they will protect and store their data.”
Stop Worrying About Data Breach Protection – Info Security Magazine
The Solution
You must boost efforts across the following:
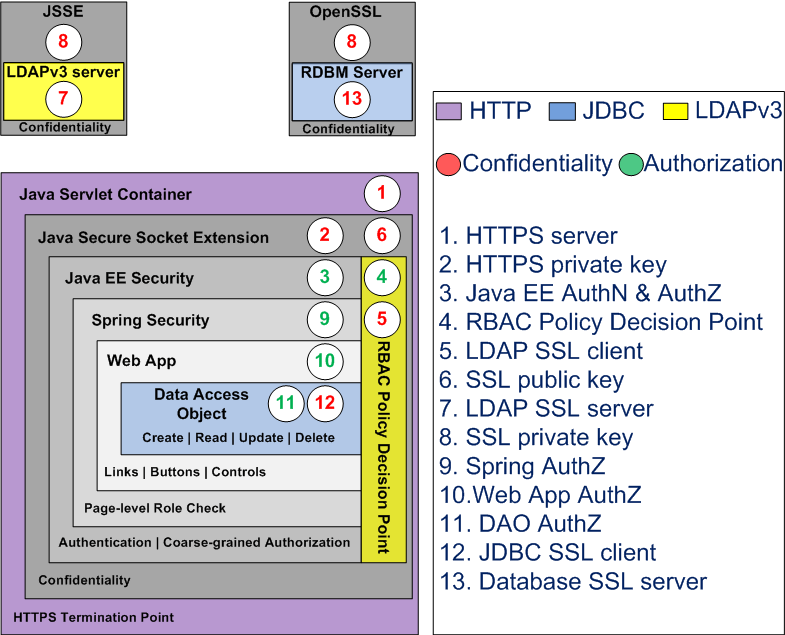
I. Authorization
The access controls commonly used today are inadequate. Let’s take a prime example: How did a low-level, government contractor download terabytes of highly sensitive data from the NSA?
“Organizations that lack these controls are vulnerable to attacks waged by individuals who have legitimate accounts on the network but seek to misuse their access for malicious purposes. This risk, known as the “insider threat” is one of the most insidious causes of data breaches.“
How to avoid the five most common causes of data breaches – Mike Chappel – Certification Magazine
Add mandatory access control checks to all interfaces connected over Internet – including those downstream of secured.
II. Audit trail
If an action is important enough to guard with a policy enforcement point, it should be logged.
“The most important step that you can take to protect your organization against improperly configured access controls is to perform regular auditing.”
How to avoid the five most common causes of data breaches – Mike Chappel – Certification Magazine
Log the resource, operation, subject id, ip, location, time, date and result.
III. Periodic Review
Circulate daily reports. Think about the results. Devise heuristic algorithms to detect anomalies automatically.
IV. Confidentiality
Encryption enabled should be the default setting for ALL network connections – even test environments. Don’t worry about the cost. Consider it cheap insurance.
“In the aftermath of security breaches at Target, Home Depot, and JP Morgan Chase, executives are reexamining their data breach risks. Hacksurfer reports on a recent survey of IT professionals that found 53 percent of organizations were investing more in data security after these high-profile cyber attacks.”
In Data Security, Compliance Isn’t Enough – Max Schleicher – TechInsurance
Encrypt data in-flight and sensitive data at rest. Hash passwords.