Defined
A set of rules surrounding the content, quality and lifecycle of a password.
What Are They For?
Helps to safeguard the integrity of password values within a particular security domain. With moves toward Multi-Factor Authentication (MFA) and other biometric authentication measures one can make the argument that the password’s days are numbered. Nevertheless they remain in use widely today and will continue for the foreseeable future.
How Do They Work?
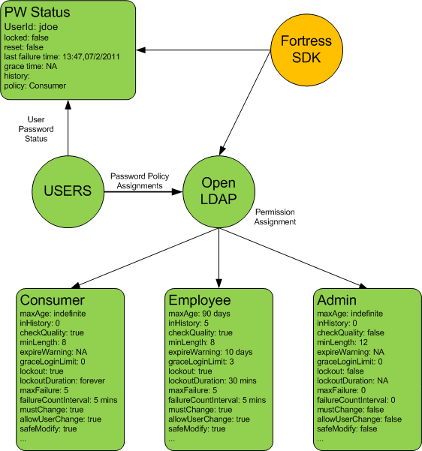
Define a set of rules to be enforced during a password lifecycle event. An example of a lifecycle event is authentication, password change and password expiration. There are a few standards that govern how systems should behave in this area.
IETF Password Policies
Apache Fortress adheres to IETF Password Policy Draft. While this draft was never formally adopted it has traction within the various directory implementations and remains the de facto standard today.
Password Policy Enforcement
Password enforcement options include:
- A configurable limit on failed authentication attempts.
- A counter to track the number of failed authentication attempts.
- A time frame in which the limit of consecutive failed authentication attempts must happen before action is taken.
- The action to be taken when the limit is reached. The action will either be nothing, or the account will be locked.
- An amount of time the account is locked (if it is to be locked) This can be indefinite.
- Password expiration.
- Expiration warning
- Grace authentications
- Password history
- Password minimum age
- Password minimum length
- Password Change after Reset
- Safe Modification of Password
- Password Policy for LDAP Directories